Ticker
Beef-XSS For Browser Exploitation
Hey guys we are come back with another excited tutorial in which we are going to introduce you with one of the most powerful tool Beef as we mention…
More InfoUndetectable Tool | FUD Metasploit Apk Generator In Linux Or Termux
If you're familiar with metasploit framework and thier features then this tools is really helpful for you and proivde you fully automate options…
More InfoPhone Number Information Gathering With PhoneInfoga Tool
Hey guys we are come back with another tutorial in which we are going to show you how to to extract details from an phone number using PhoneInfoga T…
More InfoAhmyth Tool (GUI) For Making FUD Android RAT
Hey guys we are come back with another blog post in which we are going to introduce you with a powerful tool for Windows and Linux which provide yo…
More InfoXsploitSPY For Making Lifetime Complete Access On Android Device Free
Hi guys we are come back with another powerful spyware which can make complete access on target device for lifetime and it is completely free for l…
More InfoTop Tools That Can Help You In Finding Fake AC User On Internet
The number of people who use social media is increasing day by day so the cases of online blackmailing, scams, fraud, etc. increasing. So today am …
More InfoChange MainActivity Logo Of Payload Using Any-Apk Tool
Before diving into this article, If you want to learn android hacking or ethical hacking then make sure to follow us on Instagram and subscribe to o…
More InfoHow To Sign Apk Payload With Termux
Hey guys we are come back with another excited blog post. We created many tools to modify apk payloads to make it undetectable, bind with other apk,…
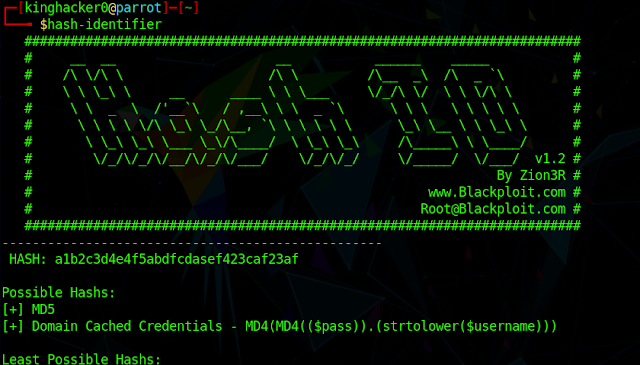
More InfoHow To Identifie And Crack Hashes In Linux
Hey guys we are come back with another excited topic of hashes and what is the main role of hashes in computer science and technology. So if you guy…
More InfoManually Create PHP Backdoor Of Metasploit
Hi guys we are come back with another tutorial in which we going to teach you how to manually create a php backdoor for metasploit and then how to e…
More InfoHow To Remotely Change Victim Android Wallpaper Screen With Kali
We are back with another Metasploit tutorial in which we going to show you how to remotely change the victim device wallpaper using Metasploit-frame…
More InfoAutomate Embed Backdoor With Apk Using Apk-Binder Tool
Hi guys we are come back with another amazing tool or script which is coded by me (github.com/kinghacker0) It helps you to bind apk files with meta…
More InfoWhat is Sql Injection ? How to Use it.
Hey guys we are come back with another excited ethical hacking post in which we going to show you what is Sql Injection and how hackers or attacker …
More InfoSqlMap For Termux (No Root)
Hi guys today am going to show you how to install SqlMap in your Termux without root. Using SqlMap you can scan and exploit different type of websit…
More InfoLatest Persistent Payload Script 2020 (100% Work)
Hello guys we come back with another exciting tutorial in which we going to teach you how to make your backdoor or payload persistent (Autostart) wi…
More InfoHunner Framework For Web Apps Pentesting
Hey guy's we are come back with another excited tutorial in which we going to introduce you one of the best web application pentesting framework…
More InfoYouTube
Popular Posts
.jpg)
See Instagram Private Account Posts & Reels Using Instanet On Linux

Extract Phone Number From Email Address Using Email2Phonenumber

WhatsApp Defendor - The WhatsApp Exploitation Framework !

Extract Passwords & Other User Credentials with LaZagne

Find Real IP Addresses Of Cloudflare Protected Websites

OSINT Emails, Websites, Instagram, etc. Using Infoooze Tool
Labels
About us
Tech consumers look to Hackersking for the latest How-To guides, Cyber Security News, Smartphones and Computer tips & tricks, etc.
admin@hackersking.co.in
Important Links
Copyright (c) 2024 Hackersking All Rights Reserved