Ticker
Scan Websites For Vulnerabilities Using WAScan Tool
Hey guy's we are come back with another excited tutorial in which we learn how to scan websites for vulnerabilities because if you find vulnerab…
More InfoMake Auto Allow All Permissions OF Any Apk
Hi guys we are come back with another excited reverse engineering tutorial in which we are going to make any apk (Payload) auto allow all permissio…
More InfoXsploitSPY For Making Lifetime Complete Access On Android Device Free
Hi guys we are come back with another powerful spyware which can make complete access on target device for lifetime and it is completely free for l…
More InfoOS-Forensics Toolkit Used By Police In Digital Investigation
Hey guy's we are come back with another blog post in which we are going to introduce you with a tool or toolkit which is used by police in digit…
More InfoFork Bomb For Crash Any Computer
There are many types of computer viruses, trojans, RATs, etc. but one of the most destructive computer viruses I have ever seen is Fork Bomb and th…
More InfoGenerate Hug Netflix Accounts For Free And Legally
Hey guy's we are come back with another excited tutorial in which we going to teach you how you can generate hug Netflix accounts in legal way.…
More InfoTop Tools That Can Help You In Finding Fake AC User On Internet
The number of people who use social media is increasing day by day so the cases of online blackmailing, scams, fraud, etc. increasing. So today am …
More InfoChange MainActivity Logo Of Payload Using Any-Apk Tool
Before diving into this article, If you want to learn android hacking or ethical hacking then make sure to follow us on Instagram and subscribe to o…
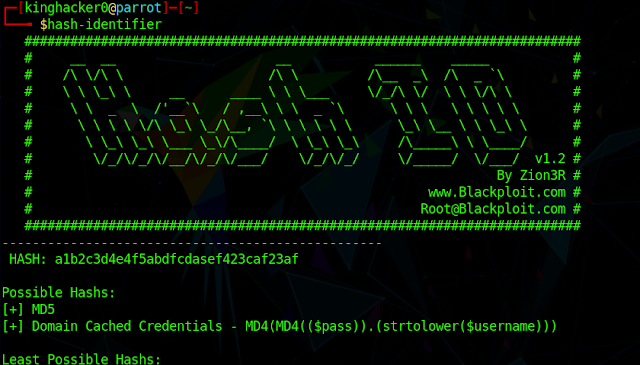
More InfoHow To Identifie And Crack Hashes In Linux
Hey guys we are come back with another excited topic of hashes and what is the main role of hashes in computer science and technology. So if you guy…
More InfoManually Create PHP Backdoor Of Metasploit
Hi guys we are come back with another tutorial in which we going to teach you how to manually create a php backdoor for metasploit and then how to e…
More InfoCrash Chrome Link List 2020
Hi guys we are come back with another excited blog post in which we going to introduce you with the list of crash chrome links which actually works…
More InfoUnlimited Free Port Forwarding Without Ngrok
Hello and welcome back friends we are come back with another excited tutorial in which we learn how to get free port forwarding without ngrok. So wi…
More InfoSpeed Up Internet By Configure APN In Android (No Root)
Hello guys we are come back with another excited tutorial in which we learn how to speed up your internet in android by configuring the APN (Access…
More InfoPerform Man In The Middle Attack With Xerosploit (Root)
Hey guy's we are come back with another excited tutorial in which we learn how to perform Man In The Middle Attack if you didn't know what i…
More InfoFsociety All In One Pen-testing Toolkit for Hackers
If you guys really like Hacking and Cracking then obviously you also heard about Mr. Robot - Web Series if you don't know then check it out it&#…
More InfoCygwin Best Alternative Of Termux For Windows
Hi ! guys we are come back with anther exited windows trick in which we show you how to get Linux Environment on your windows 7, 8 even windows Xp. S…
More InfoAuto Run USB For Copy Data Without Knowing Victim
Hackers use special USB Pen-Drive for hacking the personal or sensitive data of targeted computer. When a hacker plugin the USB drive in the victim …
More InfoHow to create windows Bootable USB Flash Drive
Today am going to show you how to create an normal USB to a Bootable USB Flash Drive which is used to install windows iso file in Computer or Laptop…
More InfoBest Spyware For Advance Remotely Access Of Android
If you want remotely control your friend, Girlfriend or child android or iso device than you are on right place today am going to show you how to …
More InfoRemove Shortcut Arrow from Desktop Icons
Hello viewers today am going to show you how to remove shortcut arrow from you desktop icons. Which give your windows unique look. So let's get …
More InfoYouTube
Popular Posts
.jpg)
See Instagram Private Account Posts & Reels Using Instanet On Linux

Extract Phone Number From Email Address Using Email2Phonenumber

WhatsApp Defendor - The WhatsApp Exploitation Framework !

Extract Passwords & Other User Credentials with LaZagne

Find Real IP Addresses Of Cloudflare Protected Websites

OSINT Emails, Websites, Instagram, etc. Using Infoooze Tool
Labels
About us
Tech consumers look to Hackersking for the latest How-To guides, Cyber Security News, Smartphones and Computer tips & tricks, etc.
admin@hackersking.co.in
Important Links
Copyright (c) 2024 Hackersking All Rights Reserved